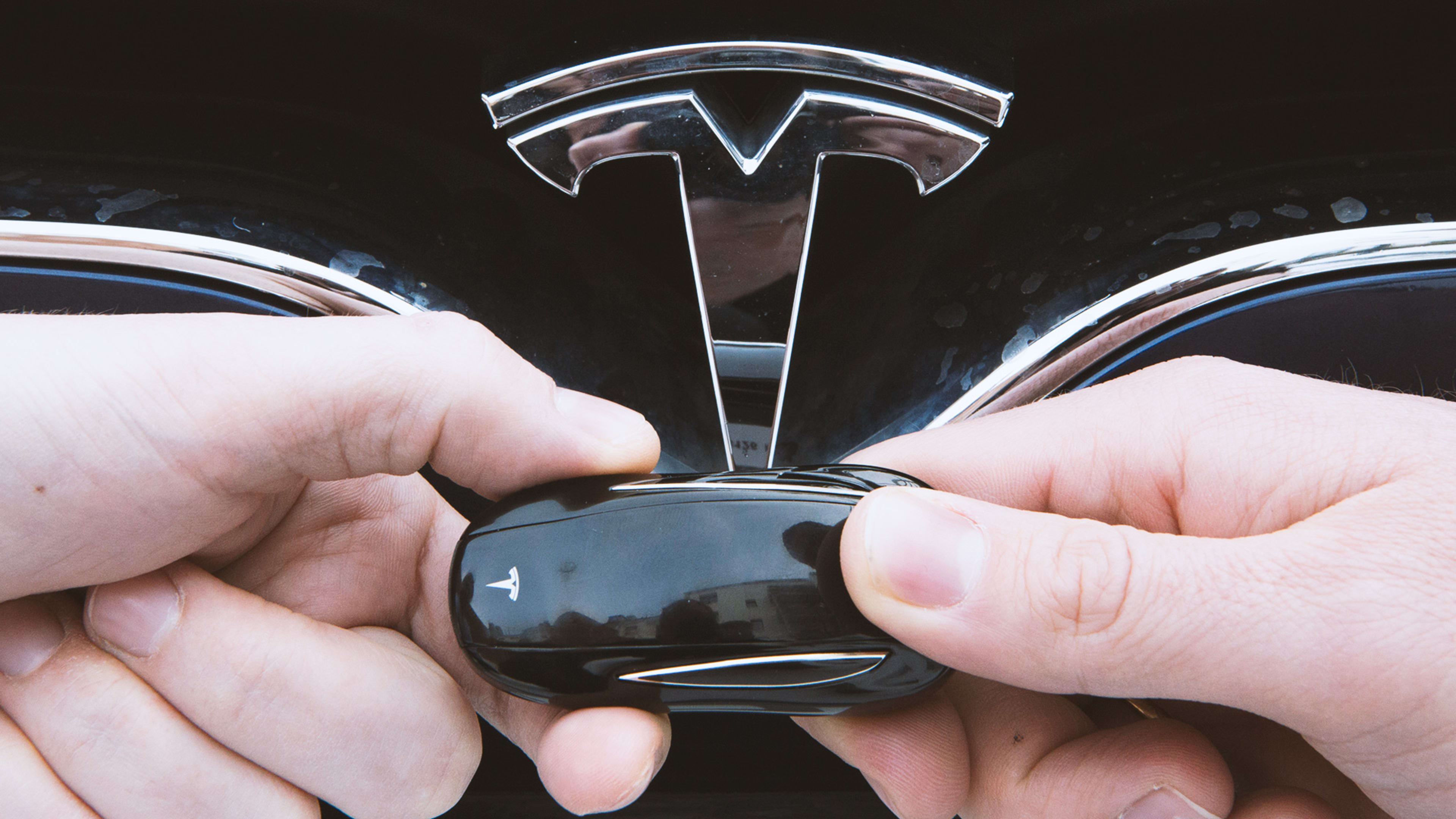
If you own a Model S and want to protect your car against theft, it’s probably time to secure your Tesla with a PIN code.
For the second time in less than a year, researchers at KU Leuven, a university in Belgium, say they’ve found a way to exploit Tesla’s keyless entry system. Last time, when the same researchers found a way to clone Tesla’s key fobs, the company upgraded its fobs’ encryption from 40-bit to 80-bit, theoretically making the system vastly more secure. But despite the upgrade, the researchers said today that they’ve found a bug in the system. The bug apparently left it only twice as hard to hack as before, a far cry from the gains the 80-bit encryption upgrade was supposed to offer, according to Wired.
Lucky for Model S owners, this time the fix apparently doesn’t involve buying yet another fob. In response to the technique described today by researcher Lennert Wouters at a security conference in Atlanta, Tesla is releasing “an over-the-air software update (part of 2019.32) that addresses this researcher’s findings and allows certain Model S owners to update their key fobs inside their car in less than two minutes,” the company said in a statement to Wired.
Tesla has a reputation for pushing out speedy software updates historically unheard-of in the auto industry. But if you’re still concerned about hackers taking off in your $75,000-plus car, you can go out of your way to turn on Tesla’s PIN-to-Drive feature, which the company name-checked in its statement today. That way, hackers would need your PIN and a cloned key to drive away.
Recognize your brand’s excellence by applying to this year’s Brands That Matter Awards before the early-rate deadline, May 3.