End-to-end encryption has become the new gold standard of online communications. With it, each party to a message uses encryption keys stored only on devices they control to encrypt one-to-one and group conversations. Apple’s iMessage, Microsoft’s Skype, the Signal messaging app, and a correctly configured account with Facebook’s WhatsApp, among other ecosystems, allow this sort of ostensibly unmonitored, uncrackable connection.
But you might note that there’s a name attached to each of those methods. While end-to-end encryption was originally envisioned as something controlled by individuals—or, in the case of business communications, by their employers—that’s not what’s materialized. Instead, because of the complexity of managing, distributing, validating, and updating encryption keys related to identity, centralization became the only game in town. That also helps explain why messaging systems are walled gardens. (Just try to send an iMessage from your WhatsApp account.)
The folks behind SecureMyEmail would like to flip that script. Their service allows user-owned, user-controlled encryption for email with apps for Mac, Windows, iPhone/iPad, and Android. It works with your existing email account—no new address required.
The service also allows seamless, key-free transmission to other SecureMyEmail subscribers and to others who use PGP software such as the PGP-compatible free-software GNU Privacy Guard.
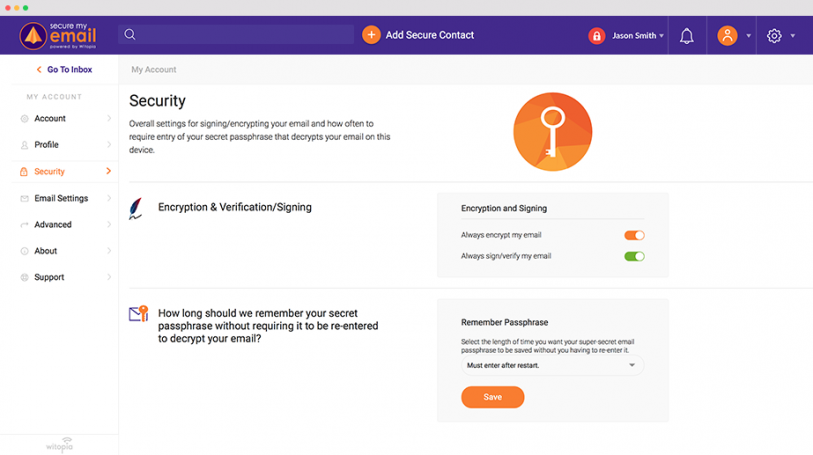
Critically, any email recipient can receive a message encrypted by SecureMyEmail without installing additional software. Subscribers create their own key or keys on their devices, which are held by the service only if a user opts in. Even then, the key is locked by a password possessed only by the subscriber.
It’s a unique approach that bridges the old and new, hiding technological complexity while bringing the heavy lifting of encryption back to the end points—the sender and receipient’s devices. It could also extend one day to other services beyond email.
Encryption without tears
“Email is wonderful as a communications tool—and everyone is scared to use it,” laments Bill Bullock, the CEO of Witopia, which released the revamped version 2 of SecureMyEmail recently. He suggests that if email were introduced today as it currently exists, it would never catch on: “Can you imagine the reviews now if email came out as an application?”
But Bullock isn’t trying to paint email as something his company can replace. That’s too tall an order for anyone, even if Slack and others have tried to displace email for business and group communications. Knowing that billions of emails are sent each day, Bullock says Witopia retooled an earlier version of SecureMyEmail, which was too restrictive. “We’re all so hungry for privacy, but we all use this thing every day,” he says of email.
Version 2 relies on existing email accounts—$30 a year for up to five accounts—with its multi-platform software acting as a combination of email client and encryption manager. (The software operates within your browser on desktop platforms, but handles encryption and decryption entirely on your device.) While this resembles GPG plug-ins available for some email clients, it’s more comprehensive, simple, and expansive. Plug-in-based solutions still require users to manage their own keys, distribute the public component to others, and find their own secure solution for recipients who don’t use GPG or PGP software.
SecureMyEmail uses its software to let a user create a key locally if they don’t have one. This is a public-private key pair, the kind used in public-key cryptography, which allows the free distribution of the public key for others to use to encrypt messages that only the recipient can decrypt. The private key is kept strictly protected and local for that decryption.
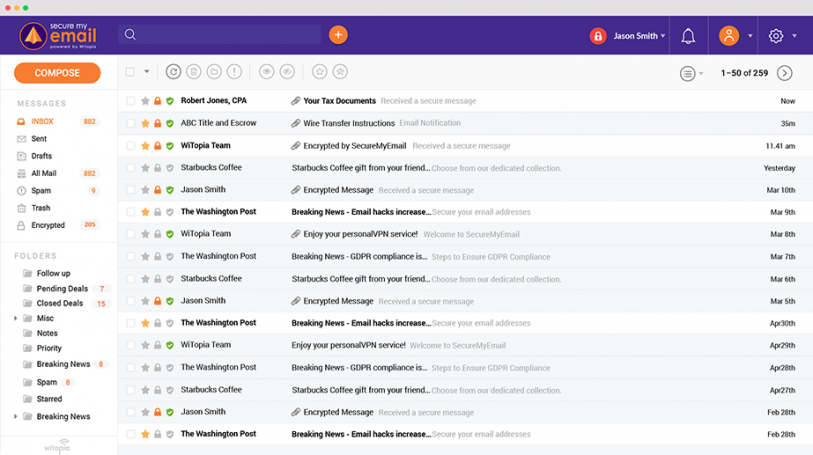
Recipients who also use SecureMyEmail—admittedly, a small number so far—can receive encrypted messages without any additional effort. Users of email clients that have plug-ins for PGP or GPG can also receive, validate, and decrypt messages from SecureMyEmail. (This makes it distinct from Protonmail, the closest competing offering. Protonmail has similar—or even higher—levels of protection and privacy, but requires use of a protonmail.com address and passes secured data through its own servers. As with SecureMyEmail, Protonmail never possesses user secrets to unlock that data.)
For everyone else, SecureMyEmail lets the sender create a password that wraps a message in strong encryption using a key that expires in a period from one hour to 31 days. The message and any attachments are encrypted locally, so your words and files never leave the device.
Recipients click on a link on the message they receive, and use an https connection to SecureMyEmail’s servers to enter the password in a browser. Once again, SecureMyEmail doesn’t receive the key; its software manages the decryption process in the browser.
PGP made better
SecureMyEmail is built atop PGP, once at the vanguard of personal encryption from its invention in the 1990s—when its creator was investigated for violating munitions export laws, but rightly never charged—and for many years thereafter. But it avoids the original version’s pitfalls and limitations.
The mechanics of PGP never got any easier.
With all that friction, secure messaging apps like iMessage, Signal, and others filled a need. They also use public-key cryptography and local key generation to create and store encryption keys so they’re only in users’ hands. They hide 100% of the overhead of encryption.
But these systems rely on an infrastructure of trust entirely owned and managed by each ecosystem’s company (or, in the case of Signal, a foundation). Commercial messaging systems are built largely or entirely on secret and proprietary code, providing many points of entry for flaws and little insight into whether attacks have occurred or been successful. A single attack could potential crack open a messaging ecosystem, at least temporarily.
Only Signal makes its code fully available for outside inspection. None of the commercial operators provide access to code or even independently contracted audited reports. The Electronic Frontier Foundation used to rate messaging systems on a variety of factors, and gave up in part because of the lack of transparency from major systems.
And despite protestations by companies that they would never revise their code and systems to allow outside monitoring, there’s nearly no way to be sure they haven’t. With repressive governments and even purported democracies—such as, well, ours—demanding access to encrypted communications, companies could be required to make silent modifications and not speak up about them, or choose not to alert the public about them.
SecureMyEmail hearkens back to a more individual-focused time by relying on PGP, which has been poked and prodded as a concept and in various implementations for nearly 30 years. PGP’s biggest flaw is how it makes you distribute your own public key, notifying people and public “keyservers” if you change it, collecting keys from others, and validating that those keys are up to date and still under the control of the person you are sending to. SecureMyEmail eliminates that rigmarole entirely. (Keybase was founded to help with key management and identity validation, but doesn’t address larger issues.)
It’s true that you still have to trust SecureMyEmail. When its software generates a PGP key, could it quietly send a copy to itself? Could it mislead you about how it handles escrow, or suffer hacks that leave its service vulnerable? Technically, it’s all possible. Bullock says the company has used outside auditors in the past and is considering it again. Over nearly 15 years, Witopia has established a track record in authentication and VPN products; it’s not a sketchy startup. It charges for its products, which means it doesn’t treat customers as a product to be sold to advertisers.
A throwback and a harbinger
Ultimately, SecureMyEmail is effectively charging for a wrapper—but what a wrapper. It’s the first service I can recall from a firm that specializes in security that allows a drop-in layer of encryption that works for all recipients, doesn’t rely on a proprietary standard or other secret sauce, and requires virtually no management on the user’s part.
That puts it in good stead to compete for privacy-minded individuals who want the option to add in security while changing nothing else about their email habits. It’s also a strong option for small businesses that need secure email for purposes such as HIPAA compliance. Bullock says the company is thinking about features for larger companies, too, and plug-ins for Apple Mail and Microsoft Outlook that would offer all the features its stand-alone client does. Potentially, there’s even room for VoIP or other types of communications within its protected bubble.
But at its heart, it’s email. Persistent and asynchronous, email is a very different beast and often preferable to live messaging, especially for attachments, group interactions, and live threading.
SecureMyEmail is, in one sense, a throwback to a time of 14.4kbps modems, when we thought naively that we could own our messages and retain our privacy. But at the same time, with the ever-growing interest in privacy and data ownership, it’s a harbinger of things to come.
Recognize your brand’s excellence by applying to this year’s Brands That Matter Awards before the early-rate deadline, May 3.
